For some time now, Identity Governance capabilities have often been in the shadow of other more in-demand features that make up Microsoft 365 packages. Even when organisations are only taking up Azure AD Premium, they will often select P1 licensing rather than P2, which means they miss out on some great Identity Governance capabilities.
Identity Governance includes a trio of services useful for managing Identity Lifecycle, Access Lifecycle and Privileged Access Management. These are all important concepts that are useful for organisations of any size, and everyone knows the benefit of self-service; in fact, a large number of are already adopting it for password resets.
With Identity Governance, we can help automate user account creation, modification and deletions via our supported HR solution of choice, as well as manage that account throughout its lifecycle with workflow approvals and regular reviews within M365 and beyond.
In this – the first of a three-part blog series – we’ll take a look at the initial HR and Application of Identity Governance. We’ll review the Access Lifecycle in our second, and Privileged Access Management in the third.
Automating Identity Lifecycle
Most organisations have either started to or have fully moved most of their primary LOB applications to SaaS models, and are using Azure AD integration to provide authentication and authorisation. This by itself is great, but still requires management overhead when a new starter comes in or leaves the organisation. Side note: if this isn’t you, consider the benefits of Conditional Access beyond Microsoft 365 and Single-Sign On capabilities for your users.
To solve this often-time-consuming workload, Microsoft’s solution within Azure AD Premium is a good fit and covers two distinct features; one for managing the relationship between a HR database to determine the onboarding or offboarding status of an account, and one for managing the relationship between Azure AD and 3rd party applications.
Between the two, we can have HR authorise the creation of a new account with a pre-configured MFA profile to allow the user to securely set a new password, followed by automatic provisioning within third-party applications that users role requires.
It’s a compelling argument and aims to massively streamline the onboarding/offboarding process when multiple applications are in the mix. The more difficult requirement, however, is that you use Azure AD for your applications AND that the 3rd party application and/or HR solution of choice support provisioning.
Choosing the correct application for you
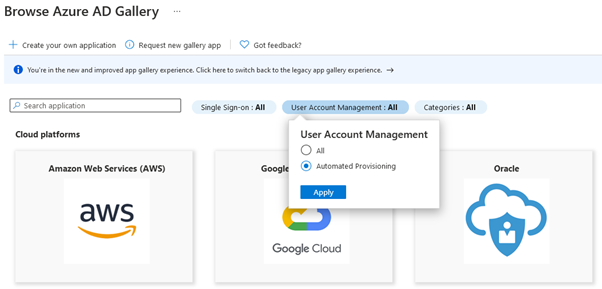
We can validate initial support for gallery applications using a relatively new filter on the primary Enterprise Application view:
The list of supported services is growing all the time; however, at the point of writing there are 219 applications, which is rather limited compared to the total of 2400 in the gallery. A lot of the big players have subscribed to this capability – including Box, Monday and Salesforce – so the rest should follow in due time. You can also integrate your own applications with the right skillset; something we may talk about in the future.
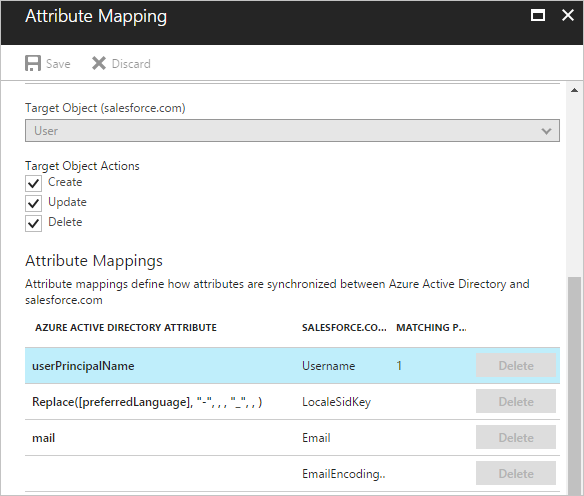
With existing applications, we can simply edit the Enterprise Application to support Automatic provisioning from Manual, and supply relevant administrator information for the third-party service. Azure AD will only manage accounts linked or created by the new configuration; everything else will remain untouched. Once we’re in, we simply manage the relevant mapping of objects and attributes accordingly; this can use simple one-to-one mapping (like below), or custom expressions to manipulate one or many attributes.
Once we have the basics of our flow configured, we need to determine if we want every single user object to be provisioned in the third-party service, possibly consuming a license. We can set up assignment scopes based on group membership or even attributes, and can configure both on the inbound provisioning into Azure AD from our HR solution of choice.
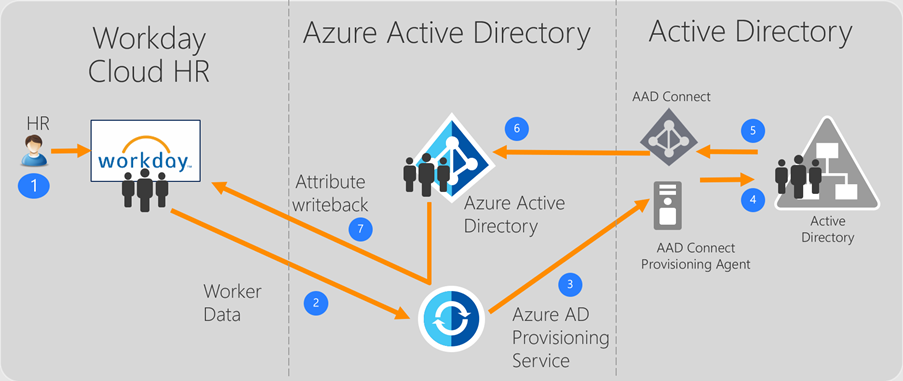
Everything so far has talked Azure AD integration, but what if you wish to also provision and manage accounts with traditional Windows Server AD too? Azure AD Connect itself has no mechanism (yet) to writeback user objects, but what we can use is the very-similarly-named Azure AD Connect Provisioning Agent.
Although this seems to only be documented for SAP SucessFactors and WorkDay, it’s an exciting option if its supported widely in the future. In the supported configuration, our supported HR solution talks directly to the Azure AD Provisioning Service, which in turn pumps our user accounts back to Windows Server AD. This in turn gets picked up by Azure AD Connect, which provisions a traditional Azure AD object for the user. Simple!
Sample design illustrating Workday provisioning via Windows Server AD
Clearly this model only applies to a few but for those that currently use Workday or SucessFactors, there is huge scope for automation.
In this blog we’ve learnt a little about Identity Lifecycle Management within Azure AD Premium, as well as a little of Access Lifecycle. In our next blog, we’ll uncover more functionality available to assist with Access Lifecycle, with Access Reviews and Entitlement Management.
George Herkes
Modern Workplace Technical Lead